Note: This is a repost of an old post I've made in 2008.
nmap is a wonderful tool specially for debugging, there are lots of times when you need to know if a port is open in a server, or maybe blocked by a firewall, or just to test your iptables rules.
Here we will learn how to use it at the command line, and using its GUI front end, nmapFE and Knmap.
Introduction
From the man page:
Nmap (“Network Mapper”) is an open source tool for network exploration and security auditing. It was designed to rapidly scan large networks, although it works fine against single hosts. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. While Nmap is commonly used for security audits, many systems and network administrators find it useful for routine tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
As you can see it is a really useful tool.
Using nmap from the console or command line
Nmap has a lot of options. We are going to focus only on some of them.
sudo nmap -sS -O 127.0.0.1
Where:
-
-sS: TCP SYN scan
-
-O: Enable Operating System detection
sudo nmap -sU 127.0.0.1
Where:
-
-sU UDP ports scan
sudo nmap -sS -O -p 20-25 127.0.0.1
Where:
-
-sS: TCP SYN scan
-
-p 20-25: Scan on ports 20 to 25
sudo nmap -sS -F 127.0.0.1
Where:
- -sS: TCP SYN scan
- -F: Fast (limited port) scan
Graphical interfaces | nmap GUI
nmap Front End (nmapFE)
This one can be installed on Linux or Mac OS X
For Ubuntu is as simple as:
sudo aptitude install nmapfe
For Mac OS X, you can compile it in your system or, use the nmapFE Mac installer
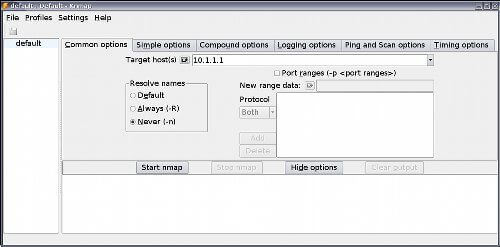
Once installed, it will look like this:
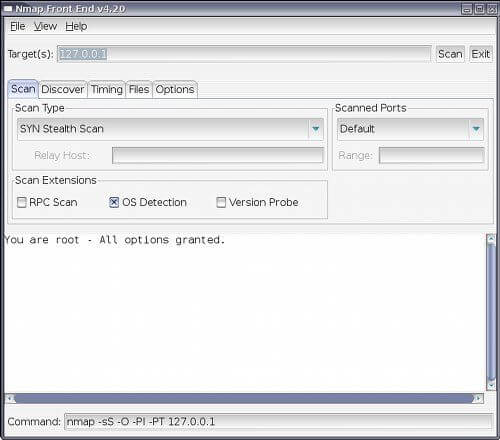
On target you put the IP or IPs you want to scan, select the scan type, if you want TCP SYN, UDP, Connect scan, or other, the most used are SYN and UDP. If you want to scan for UDP ports. Also select the scanned ports, you can scan the default ones, All, fast (only the ports in nmap-services file).
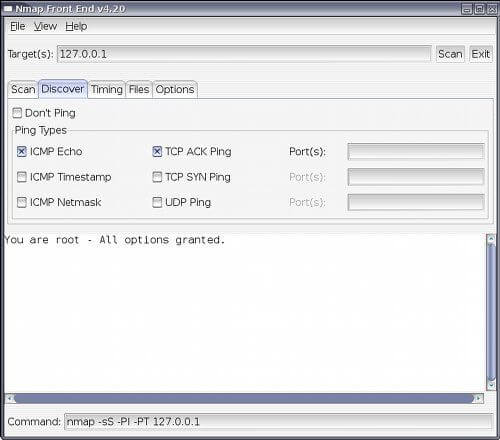
Select if you want to use the discovery option, if you want to ping and which type of ping you want to use to discover network nodes if you have specified an IP range to scan.
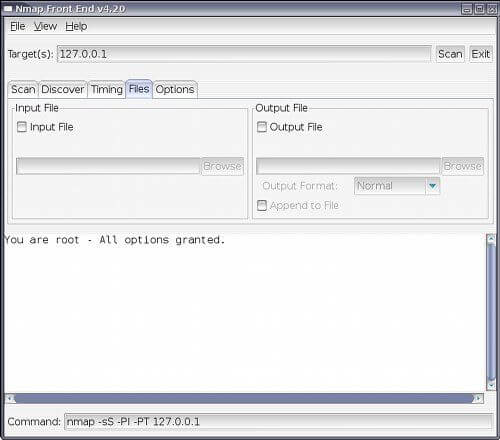
Useful if you want to send the output to a file.
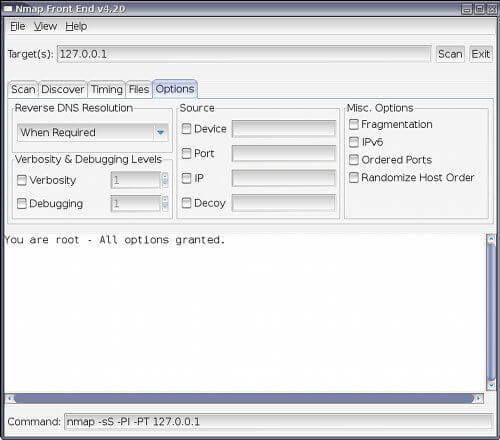
Lots of other tools, if you want you can enable verbosity of debugging, and if you want IPv6 support.
KDE Nmap (knmap)
This is only for Linux.
For ubuntu and specially if you are using KDE (kubuntu) run:
sudo aptitude install knmap
Its interface has divided the options in a very convenient way. In the common options you will see the target IPs, the port range and if you want it to resolve names.
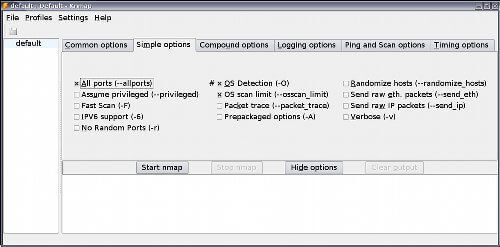
Here you select if you want to scan all ports, perform a fast scan, IPv6 support, Operating System detection, verbose, and other options.
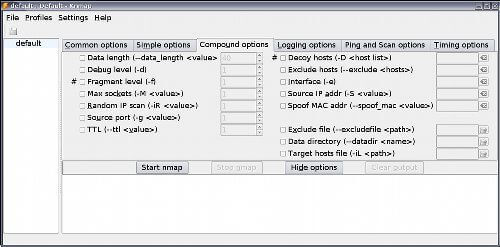
In compound options, you will find a lot more options to play with, you can select which interface to use, which IP, and even if you want to spoof your Mac address!
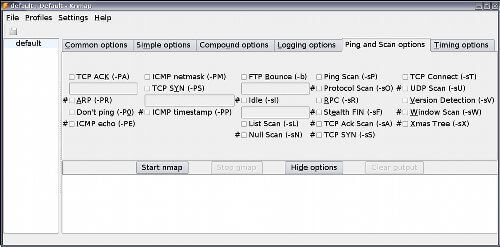
Ping and scan options is like the discover and the scan tabs of nmapFE together.
Zenmap
Zenmap is another nmap GUI front end, I'm currently using it on my Arch Linux PC as well as with my Mac laptop.
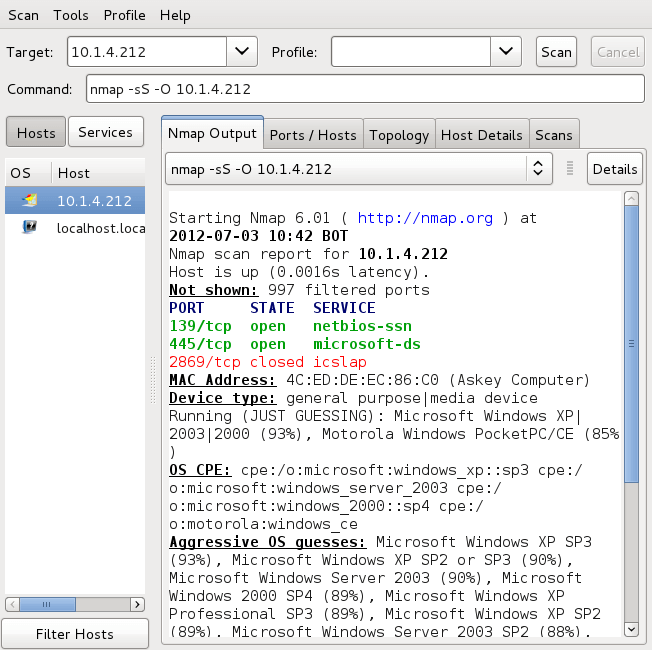
Conclusion
Nmap is a must have tool for network and security administrators. Using its GUI frontend you will find good and easy ways to use them, and also to learn how to use them, because you can discover new applications. With nmapFE you can see the command that is going to be executed, another good point for knmap is that it has the possibility to save profiles, with all the options you have enabled, so your next scan is easier.
This is a tool you must master, and no matter if you are running Linux or Mac, you have it disposable.